Vulnerability management solution


With vulnerabilities more widespread than ever before it’s critical to be able to quickly weed through and prioritize these risks based how they impact the key applications that run your business. Yet vulnerability information is typically presented in technical terms such as servers and IP addresses, which is not a meaningful format for business application owners.
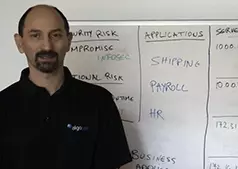
AlgoSec seamlessly integrates with the leading vulnerability scanners to map vulnerabilities directly to their business applications, including servers and complex connectivity flows, and provide a security rating for every business application. AlgoSec automatically recalculates these risk scores whenever a change is made through its intelligent, automated security policy change management process, to ensure that you always have an up-to-date, business-centric view of your risk. With this information you can effectively prioritize and remediate risk across your organization based on its criticality and impact on your business.
Learn from the experts. Get the latest industry insights